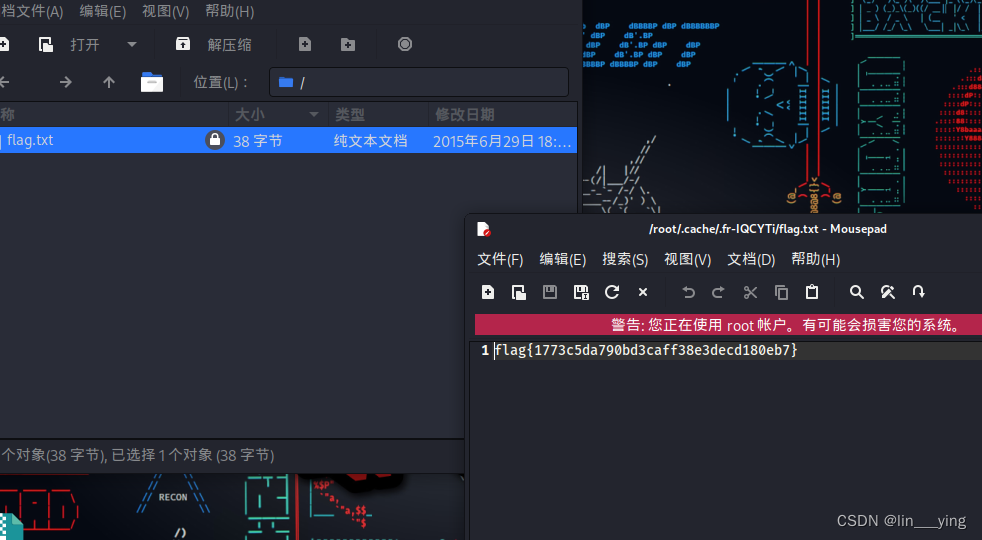
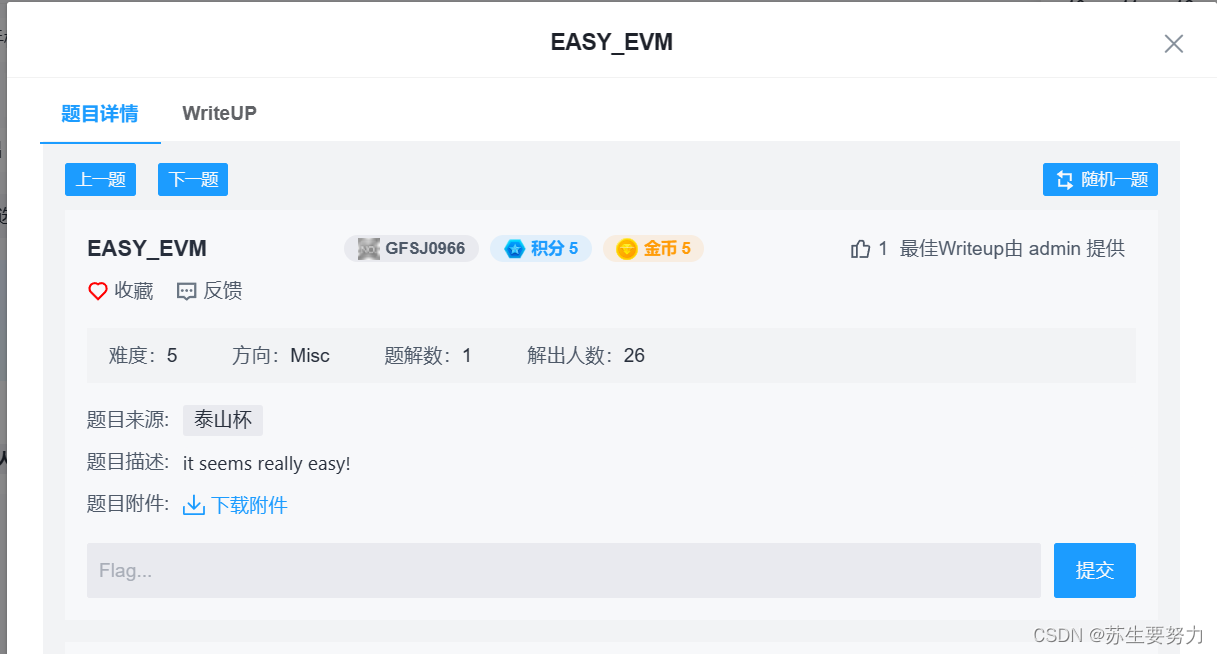
题目链接:攻防世界 (xctf.org.cn)
下载附件得到info.txt:
pragma solidity ^0.5.0;
ABI:
[
{
"inputs": [],
"payable": true,
"stateMutability": "payable",
"type": "constructor"
},
{
"constant": true,
"inputs": [
{
"internalType": "string",
"name": "source",
"type": "string"
}
],
"name": "Convert",
"outputs": [
{
"internalType": "uint256",
"name": "result",
"type": "uint256"
}
],
"payable": false,
"stateMutability": "pure",
"type": "function"
},
{
"constant": true,
"inputs": [],
"name": "GetFlag",
"outputs": [
{
"internalType": "string",
"name": "flag",
"type": "string"
}
],
"payable": false,
"stateMutability": "view",
"type": "func tion"
},
{
"constant": true,
"inputs": [],
"name": "Require",
"outputs": [],
"payable": false,
"stateMutability": "view",
"type": "function"
}
]
Bytecode:
6080604052693100e35e552c1273c953600181905550691ac3243c9e81ba850045600281905550695ce6a91010e307946b8760038190555061030f806100466000396000f3fe608060405234801561001057600080fd5b24506004361060415760003560e01c80638906899514610046578063907e178b146100c9578063b357e2cd14610198575b600080fd5b61004e6101a2565b6040518080602001828103825283818151815260200191508051906020019080838360005b8381101561008e578082015181840152602081019050610073565b50505050905090810190601f1680156100bb5780820380516001836020036101000a031916815260200191505b509250505060405180910390f35b610182600480360360208110156100df57600080fd5b81019080803590602001906401000000008111156100fc57600080fd5b82018360208201111561010e57600080fd5b8035906020019184600183028401116401000000008311171561013057600080fd5b91908080601f016020809104026020016040519081016040528093929190818152602001838380828437600081840152601f19601f8201169050808301925050505050505091929192905050506101ac565b6040518082815260200191505060405180910390f35b6101a06101cd565b005b6060600054905090565b600080602083015190506101008160001c816101c457fe5b04915050919050565b600061027260008054600181600116156101000203166002900480601f0160208091040260200160405190810160405280929190818152602001828054600181600116156101000203166002900480156102685780601f1061023d57610100808354040283529160200191610268565b820191906000526020600020905b81548152906001019060200180831161024b57829003601f168201915b50505050506101ac565b905069291012e74c77fb9b1133600154828161028a57fe5b061461029557600080fd5b690c9158ba60d3e58402f560025482816102ab57fe5b06146102b657600080fd5b69208474a0eb40ca8d322560035482816102cc57fe5b06146102d757600080fd5b5056fea265627a7a7231582076bf9599d7c1db3c967349730ba966ea19a3c19a82c194cf481bf5dd993fec0d64736f6c63430005110032
这是一个以太坊智能合约(EVM)虚拟机的 Bytecode,那么考察的就是EVM逆向。不会做,告辞。
查了一下WP,Bytecode 被修改过使其无法反编译,需要修复或者直接看opcode。WP给出的源码长这样:
pragma solidity ^0.5.0;
contract EASY_EVM_CRYPTO{
// flag = "flag{An_E4sy_EVM_y0u_sO1ve_it!}"
string private FLAG;
uint private x;
uint private y;
uint private z;
// flag = 0x666c61677b416e5f453473795f45564d5f7930755f734f3176655f6974217d
constructor() public payable {
x = 231412341286754812414291;
y = 126381254785148123414597;
z = 438712649816519864511367;
}
function GetFlag() public view returns (string memory flag) {
assembly {
flag := sload(0)
}
}
function Convert(string memory source) public pure returns (uint result) {
bytes32 tmp;
assembly {
tmp := mload(add(source, 32))
}
result = uint(tmp) / 0x100;
}
function Require() public view {
uint tmp = Convert(FLAG);
require(tmp%x == 193913535844325315514675);
require(tmp%y == 59349569214207838388981);
require(tmp%z == 153559101645126489682469);
}
}
那么这实际上是一个求解同余方程组的数论问题。
试着把数论部分做一下,sage脚本:
from Crypto.Util.number import *
x = 231412341286754812414291
y = 126381254785148123414597
z = 438712649816519864511367
rx = 193913535844325315514675
ry = 59349569214207838388981
rz = 153559101645126489682469
m = crt([rx, ry, rz], [x, y, z])
while b'flag' not in long_to_bytes(m):
m += x * y * z
print(long_to_bytes(m))运行后得到flag:flag{An_E4sy_EVM_y0u_sO1ve_it!}